Office software used to be simple. You wrote documents, built spreadsheets, maybe created a presentation if you were feeling ambitious. Now, office software is a fully connected ecosystem powered by cloud computing, artificial intelligence, and collaboration tools that never sleep.
And with all that convenience comes something humans consistently underestimate: risk.
Best Office Productivity Software in 2026
Office software security is no longer just about antivirus programs and strong passwords. It now involves identity management, cloud security, data governance, AI risks, and user behavior. One careless click can expose sensitive business data, financial records, or entire company infrastructures.
This guide breaks down everything you need to know about securing office software in 2026. Whether you’re an individual user, a startup founder, or managing an enterprise, understanding these concepts is no longer optional.
1. What Is Office Software Security?
Office software security refers to the measures, tools, and practices used to protect data, users, and systems within productivity platforms like word processors, spreadsheets, email clients, and collaboration tools.
Core Areas:
- Data protection
- User authentication
- Application security
- Cloud infrastructure security
- Compliance and governance
Modern office environments are deeply integrated, meaning a vulnerability in one tool can affect the entire ecosystem.
2. Why Office Software Security Matters More Than Ever
If you think your documents are boring and no one cares, congratulations, you’re exactly the kind of target attackers love.
Key Reasons:
- Increased remote work
- Cloud-based storage
- Integration with third-party apps
- AI-driven automation
Real Risks:
- Data breaches
- Financial loss
- Reputation damage
- Legal consequences
3. Common Threats in Office Software
3.1 Phishing Attacks
Phishing remains the most common attack vector. Attackers impersonate trusted entities to steal login credentials.
3.2 Malware and Ransomware
Malicious files embedded in documents can infect systems.
3.3 Insider Threats
Sometimes the biggest risk is already inside your organization.
3.4 Weak Passwords
Still happening in 2026. Still a terrible idea.
3.5 Unauthorized Access
Improper permissions can expose sensitive data.
4. Cloud Security in Office Software
Most modern office tools operate in the cloud, which introduces both flexibility and risk.
Key Concepts:
- Shared responsibility model
- Data encryption
- Secure APIs
Best Practices:
- Use trusted providers
- Enable encryption
- Monitor access logs
5. Identity and Access Management (IAM)
IAM ensures that only authorized users can access specific resources.
Components:
- Multi-factor authentication (MFA)
- Single sign-on (SSO)
- Role-based access control (RBAC)
Why It Matters:
Controlling who can access what is the foundation of security.
6. Data Encryption and Protection
Encryption converts data into unreadable formats for unauthorized users.
Types:
- Data at rest
- Data in transit
Tools:
- End-to-end encryption
- Secure key management
7. Secure Collaboration Practices
Collaboration tools are convenient, but they can also expose data.
Risks:
- Public sharing links
- Unrestricted editing access
Solutions:
- Permission controls
- Expiration dates for links
8. AI Security Risks in Office Software
AI is helpful, but it also introduces new vulnerabilities.
Risks:
- Data leakage
- Prompt injection attacks
- Bias and manipulation
Mitigation:
- Limit sensitive inputs
- Monitor AI outputs
9. Endpoint Security
Devices accessing office software must be secure.
Includes:
- Laptops
- Smartphones
- Tablets
Measures:
- Device encryption
- Security updates
10. Compliance and Regulations
Organizations must comply with data protection laws.
Examples:
11. Backup and Recovery Strategies
Even with strong security, things can go wrong.
Best Practices:
- Regular backups
- Version history
- Disaster recovery plans
12. Security in Email Systems
Email remains a major vulnerability.
Risks:
Solutions:
- Spam filters
- Email authentication protocols
13. Third-Party Integrations
Office software often connects with external apps.
Risks:
- Data exposure
- Weak API security
14. User Training and Awareness
Humans are the weakest link. Consistently.
Focus Areas:
- Recognizing phishing
- Secure password habits
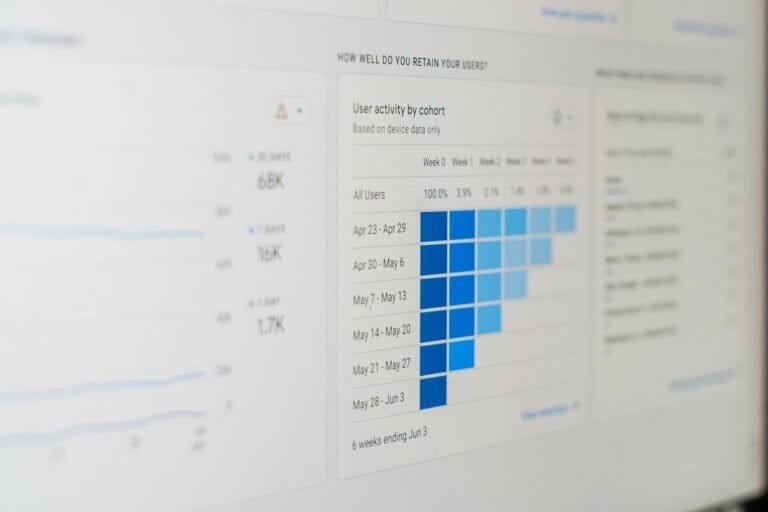
15. Security Monitoring and Auditing
Continuous monitoring helps detect threats early.
16. Zero Trust Security Model
Trust no one. Verify everything.
17. Mobile Security Challenges
Mobile access introduces additional risks.
18. Secure File Sharing
Control how files are shared and accessed.
19. Password Management Tools
Use password managers to avoid chaos.
20. Multi-Layered Security Approach
Combine multiple security measures.
21. Incident Response Planning
Prepare for security incidents before they happen.
22. Future Trends in Office Software Security
Trends:
- AI-driven security
- Behavioral analytics
- Automated threat detection
23. Best Practices Checklist
- Enable MFA
- Use strong passwords
- Regular updates
- Monitor activity
24. Tools for Office Security
Popular Platforms:
- Microsoft 365 Security
- Google Workspace Security
- Endpoint protection tools
25. Final Thoughts
Office software security is not optional anymore. It is a necessity in a world where data is constantly under threat.
Ignoring security is like leaving your front door open and hoping no one walks in. Sometimes you get lucky. Most times, you don’t.
The good news is that with the right strategies, tools, and awareness, you can significantly reduce risks and protect your digital workspace.
FAQs
What is office software security?
It refers to protecting data and systems within productivity tools.
Why is it important?
Because cyber threats are increasing.
What are the biggest risks?
Phishing, malware, and weak passwords.
How can I improve security?
Use MFA, strong passwords, and secure practices.