Developers love tools. IDEs, CI/CD pipelines, package managers, container platforms, cloud dashboards—if it promises speed or convenience, it gets installed. Unfortunately, every shiny tool also expands your attack surface.
In 2026, software development is deeply interconnected. Your code depends on hundreds of third-party libraries, your builds run in the cloud, and your deployments are automated across multiple environments. That’s efficient. It’s also fragile if security is treated as an afterthought.
Developer tools are no longer just productivity enhancers—they are critical parts of your security infrastructure. A compromised tool can expose secrets, inject malicious code, or bring down entire systems.
This guide covers the best practices for securing developer tools, from local environments to cloud pipelines, helping teams reduce risk without slowing down development.
Why Developer Tool Security Matters
Modern development workflows rely on trust—trust in tools, dependencies, and automation. That trust is often misplaced.
Rising Threat Landscape
Recent years have seen a surge in:
- Supply chain attacks
- Dependency hijacking
- Credential leaks in repositories
- CI/CD pipeline compromises
Attackers target developer tools because they provide high leverage. Compromise one tool, and you potentially compromise everything built with it.
Real Impact
A single exposed API key or compromised dependency can lead to:
- Data breaches
- Financial loss
- Reputation damage
- Regulatory penalties
Security isn’t optional anymore—it’s foundational.
Core Principles of Developer Tool Security
1. Least Privilege Access
Every tool, service, and user should only have the permissions they absolutely need.
- Avoid admin-level access by default
- Use role-based access control (RBAC)
- Regularly audit permissions
2. Zero Trust Approach
Never assume anything is safe just because it’s inside your network.
- Verify every request
- Authenticate continuously
- Monitor activity in real time
3. Defense in Depth
Layer your security controls so that if one fails, others still protect you.
- Endpoint security
- Network controls
- Application-level protections
Securing Local Development Environments
Developers’ machines are often the weakest link.
Best Practices
- Use encrypted disks
- Keep operating systems and tools updated
- Install software only from trusted sources
- Avoid using personal devices for sensitive work
Secrets Management
Never store secrets in plain text.
- Use environment variables or secret managers
- Avoid hardcoding credentials
- Rotate keys regularly
Securing Code Repositories
Your repository is your source of truth—and a prime target.
Access Control
- Enforce strong authentication (MFA)
- Limit access based on roles
- Remove inactive users
Code Scanning
- Use automated tools to detect vulnerabilities
- Scan for exposed secrets
- Enforce secure coding standards
Branch Protection
- Require pull request reviews
- Prevent direct commits to main branches
- Enforce status checks before merging
Dependency and Package Security
Modern applications rely heavily on third-party packages.
Risks
- Malicious packages
- Outdated libraries with vulnerabilities
- Dependency confusion attacks
Best Practices
- Use trusted registries
- Pin dependency versions
- Regularly update dependencies
- Use software composition analysis (SCA) tools
CI/CD Pipeline Security
CI/CD pipelines automate builds and deployments—but they also automate mistakes.
Secure Configuration
- Store secrets securely
- Use isolated environments
- Restrict access to pipelines
Monitoring and Logging
- Track pipeline activity
- Detect anomalies
- Maintain audit logs
Artifact Integrity
- Verify build artifacts
- Use checksums and signatures
Cloud and Infrastructure Security
Most developer tools now operate in the cloud.
Identity and Access Management (IAM)
- Use least privilege policies
- Enable MFA
- Monitor access logs
Network Security
- Use private networks
- Restrict inbound and outbound traffic
- Implement firewalls
Configuration Management
- Avoid misconfigurations
- Use infrastructure as code (IaC)
- Regularly audit configurations
Container and Kubernetes Security
Containers are everywhere, which means so are their vulnerabilities.
Best Practices
- Use minimal base images
- Scan images for vulnerabilities
- Avoid running containers as root
Kubernetes Security
- Secure API access
- Use network policies
- Monitor cluster activity
API and Integration Security
APIs connect everything—and expose everything if not secured.
Best Practices
- Use authentication and authorization
- Implement rate limiting
- Validate inputs
Monitoring and Incident Response
Security isn’t just prevention—it’s detection and response.
Monitoring
- Use centralized logging
- Set up alerts for suspicious activity
Incident Response
- Define response plans
- Conduct regular drills
- Document incidents and lessons learned
Security Culture and Training
Tools alone don’t secure systems—people do.
Best Practices
- Train developers on secure coding
- Encourage security awareness
- Integrate security into development workflows
Common Mistakes to Avoid
1. Ignoring Updates
Outdated tools are vulnerable tools.
2. Over-Permissioned Access
Too many permissions increase risk.
3. Hardcoding Secrets
Still happening. Still a bad idea.
4. Lack of Monitoring
You can’t fix what you don’t see.
Future Trends in Developer Tool Security
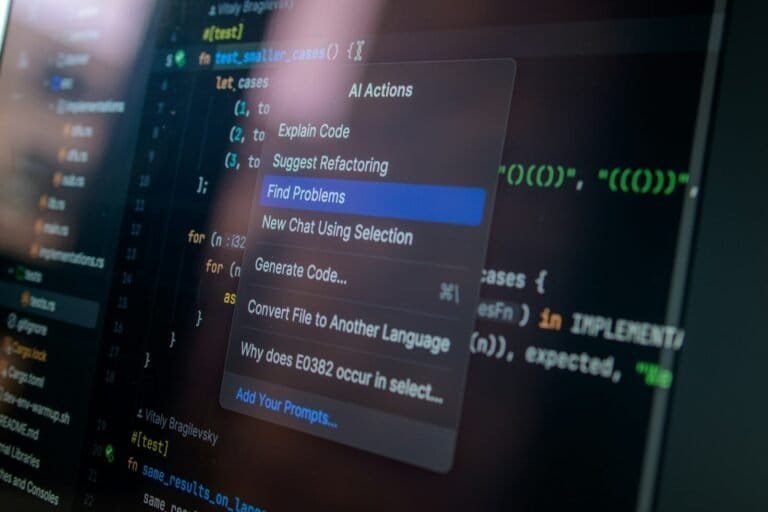
1. AI-Driven Security
AI is being used to detect vulnerabilities and automate responses.
2. DevSecOps Adoption
Security is integrated into every stage of development.
3. Supply Chain Security Focus
Greater emphasis on securing dependencies and build pipelines.
Conclusion
Developer tool security is no longer optional—it’s essential. As development ecosystems grow more complex, so do the risks.
By following best practices—securing local environments, managing dependencies, protecting pipelines, and fostering a security-first culture—teams can build resilient systems without sacrificing productivity.
Because in the end, the fastest way to ship software is still slower than recovering from a breach.
FAQs
1. What is developer tool security?
Developer tool security refers to protecting the tools and environments used in software development from vulnerabilities, unauthorized access, and attacks.
2. Why is CI/CD security important?
CI/CD pipelines automate code deployment, making them a high-value target for attackers. Securing them prevents unauthorized changes and data breaches.
3. How can I secure my development environment?
Use encryption, keep systems updated, avoid storing secrets in plain text, and restrict access to sensitive resources.
4. What is a supply chain attack?
A supply chain attack targets third-party dependencies or tools to compromise software during development or deployment.
5. What is DevSecOps?
DevSecOps integrates security practices into the software development lifecycle, ensuring security is addressed at every stage.